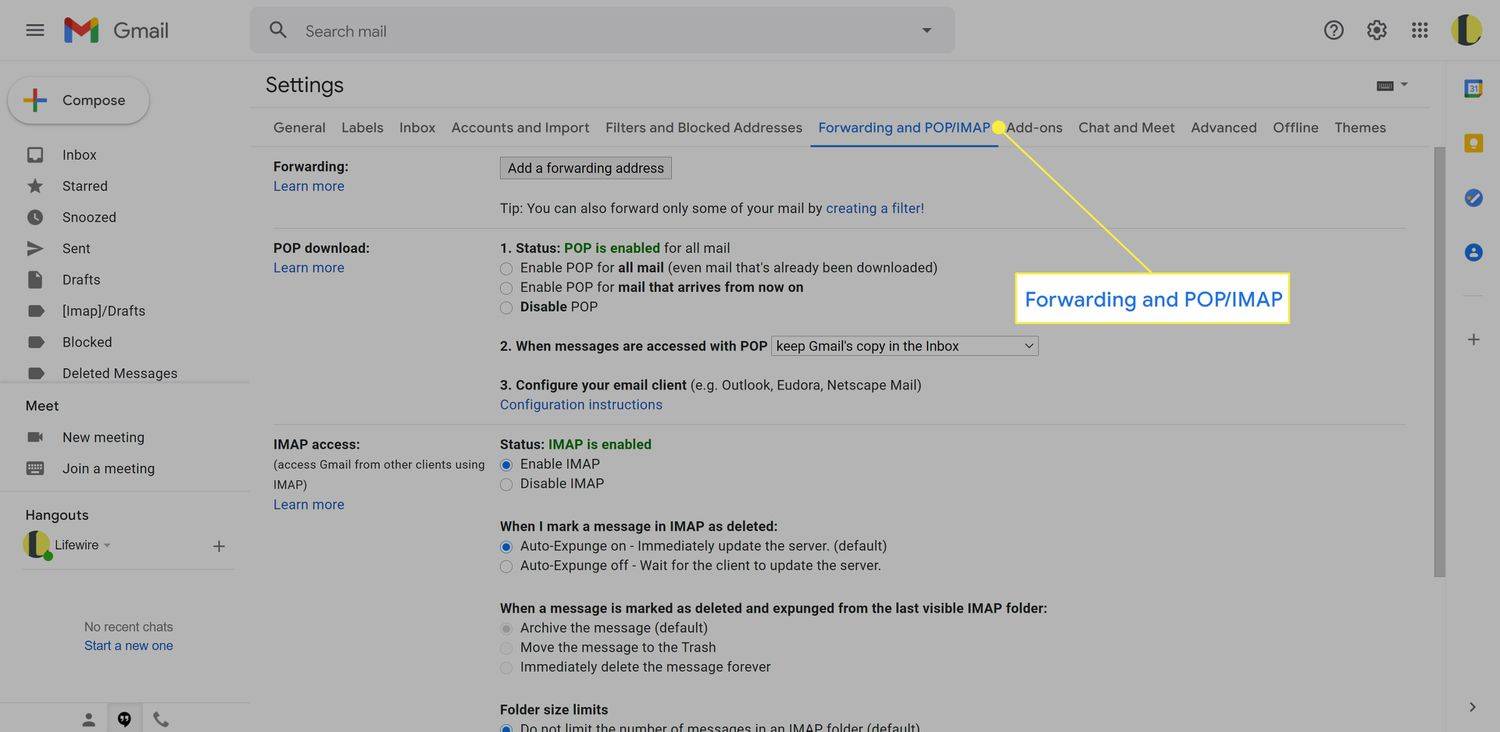
Nikomur, ki uporablja Windows 10, ni skrivnost, da ta operacijski sistem zbira veliko zasebnih informacij in jih pošilja nazaj Microsoftu, da dobi več telemetričnih podatkov. Številni uporabniki niso zadovoljni, da jih Windows 10 vohuni in nenehno išče način, kako to ustaviti. Čeprav se prvič sklicujemo na to težavo, bi danes rad delil drugačen način, da Windows 10 prepreči zbiranje vaših občutljivih podatkov z uporabo samo vgrajenega požarnega zidu Windows.
Oglas
V prejšnjem članku Kako onemogočiti telemetrijo in zbiranje podatkov v sistemu Windows 10 , Na splošno sem opisal, kaj je telemetrija in kako Microsoft zbira vaše podatke. Poleg tega članek vsebuje rešitev proti zbiranju podatkov brez vaše odobritve.
Preden začnemo, moram vsekakor omeniti eno dejstvo. Pazite se uporabnikov operacijskega sistema Windows 7 / Windows 8, tudi vaš operacijski sistem vas morda vohuni! Glej naslednji članek: Telemetrija in zbiranje podatkov prihajata tudi v Windows 7 in Windows 8
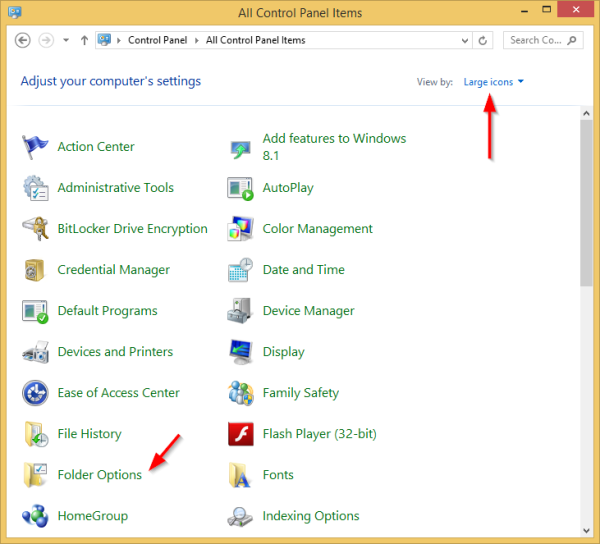
Zdaj pa poglejmo, kaj lahko storimo, da preprečimo, da vas Windows 10 ne bi vohunil z uporabo samo požarnega zidu Windows. Glavna ideja te metode je blokiranje dobro znanega seznama Microsoftovih strežnikov z uporabo ustreznih pravil požarnega zidu Windows. To v postopek ne vključuje nobenega orodja tretje osebe, kar je prav tako dobro. Videli boste in nadzorovali, kaj počnete.
Poglejmo naslednji primer:
kako spremeniti svoj privzeti google račun -
netsh advfirewall firewall add rule name = 'telemetry_watson.telemetry.microsoft.com' dir = out action = block remoteip = 65.55.252.43,65.52.108.29 enable = yes
Zgornji ukaz doda in aktivira novo pravilo, ki blokira odhodne povezave s strežnikom 'telemetry_watson.telemetry.microsoft.com'. Blokiranje bo izvedeno s pomočjo naslednjih naslovov IP: 65.55.252.43,65.52.108.29.
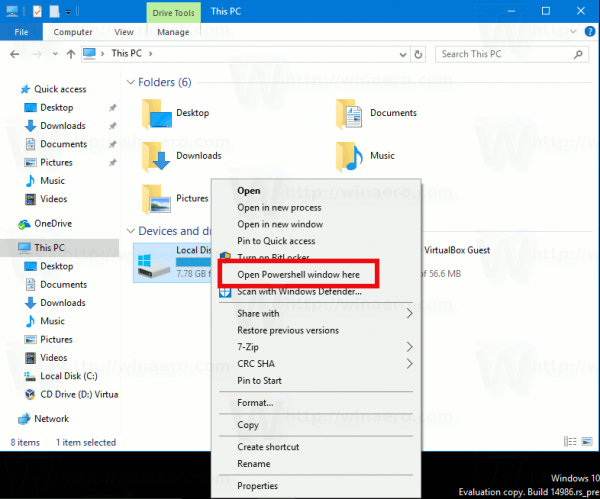
Ta ukaz je treba izvesti v povišanem ukaznem pozivu. To ni pretežko. Ko pa morate blokirati vse telemetrične strežnike, se lahko utrudite, če zaženete vse zahtevane ukaze enega za drugim. Poglejte celoten seznam (delček PowerShell) spodaj!
Set-NetFirewallProfile -all netsh advfirewall firewall add rule name name = 'telemetry_vortex.data.microsoft.com' dir = out action = block remoteip = 191.232.139.254 enable = yes netsh advfirewall firewall add rule name = 'telemetry_telecommand.telemetry.microsoft.com 'dir = out action = block remoteip = 65.55.252.92 enable = yes netsh advfirewall firewall add rule name =' telemetry_oca.telemetry.microsoft.com 'dir = out action = block remoteip = 65.55.252.63 enable = yes netsh advfirewall firewall add rule name = 'telemetry_sqm.telemetry.microsoft.com' dir = out action = block remoteip = 65.55.252.93 enable = yes netsh advfirewall firewall add rule name = 'telemetry_watson.telemetry.microsoft.com' dir = out action = block remoteip = 65.55 .252.43,65.52.108.29 enable = yes netsh advfirewall firewall add rule name = 'telemetry_redir.metaservices.microsoft.com' dir = out action = block remoteip = 194.44.4.200,194.44.4.208 enable = yes netsh advfirewall firewall add name name = 'telemetry_choice.microsoft.com' dir = out action = block remoteip = 157.56.91.77 sl able = yes netsh advfirewall firewall add rule name = 'telemetry_df.telemetry.microsoft.com' dir = out action = block remoteip = 65.52.100.7 enable = yes netsh advfirewall firewall add rule name = 'telemetry_reports.wes.df.telemetry.microsoft .com 'dir = out action = block remoteip = 65.52.100.91 enable = yes netsh advfirewall firewall add rule name =' telemetry_wes.df.telemetry.microsoft.com 'dir = out action = block remoteip = 65.52.100.93 enable = yes netsh advfirewall firewall add rule name = 'telemetry_services.wes.df.telemetry.microsoft.com' dir = out action = block remoteip = 65.52.100.92 enable = yes netsh advfirewall firewall add rule name = 'telemetry_sqm.df.telemetry.microsoft.com 'dir = out action = block remoteip = 65.52.100.94 enable = yes netsh advfirewall firewall add rule name =' telemetry_telemetry.microsoft.com 'dir = out action = block remoteip = 65.52.100.9 enable = yes netsh advfirewall firewall add name rule = 'telemetry_watson.ppe.telemetry.microsoft.com' dir = out action = block remoteip = 65.52.100.11 enable = yes netsh advfirewall firewall dodaj pravilo ime = 'telemetry_telemetry.appex.bing.net' dir = out action = block remoteip = 168.63.108.233 enable = yes netsh advfirewall firewall add rule name = 'telemetry_telemetry.urs.microsoft.com' dir = out action = block remoteip = 157.56.74.250 enable = yes netsh advfirewall firewall add rule name = 'telemetry_settings-sandbox.data.microsoft.com' dir = out action = block remoteip = 111.221.29.177 enable = yes netsh advfirewall firewall add rule name = 'telemetry_vortex- sandbox.data.microsoft.com 'dir = out action = block remoteip = 64.4.54.32 enable = yes netsh advfirewall firewall add rule name =' telemetry_survey.watson.microsoft.com 'dir = out action = block remoteip = 207.68.166.254 enable = da netsh advfirewall firewall dodaj pravilo ime = 'telemetry_watson.live.com' dir = out action = block remoteip = 207.46.223.94 enable = yes netsh advfirewall firewall add rule name = 'telemetry_watson.microsoft.com' dir = out action = block remoteip = 65.55.252.71 enable = yes netsh advfirewall firewall add rule name = 'telemetry_statsfe2.ws.microsoft. com 'dir = out action = block remoteip = 64.4.54.22 enable = yes netsh advfirewall firewall add rule name =' telemetry_corpext.msitadfs.glbdns2.microsoft.com 'dir = out action = block remoteip = 131.107.113.238 enable = yes netsh advfirewall firewall add rule name = 'telemetry_compatexchange.cloudapp.net' dir = out action = block remoteip = 23.99.10.11 enable = yes netsh advfirewall firewall add rule name = 'telemetry_cs1.wpc.v0cdn.net' dir = out action = block remoteip = 68.232.34.200 enable = yes netsh advfirewall firewall add rule name = 'telemetry_a-0001.a-msedge.net' dir = out action = block remoteip = 204.79.197.200 enable = yes netsh advfirewall firewall add rule name = 'telemetry_statsfe2.update. microsoft.com.akadns.net 'dir = out action = block remoteip = 64.4.54.22 enable = yes netsh advfirewall firewall add rule name =' telemetry_sls.update.microsoft.com.akadns.net 'dir = out action = block remoteip = 157.56.77.139 enable = yes netsh advfirewall firewall add rule name = 'telemetry_fe2.update.microsoft.com.akadns.net' dir = out action = block remot eip = 134.170.58.121,134.170.58.123,134.170.53.29,66.119.144.190,134.170.58.189,134.170.58.118,134.170.53.30,134.170.51.190 enable = yes netsh advfirewall firewall add rule name = 'telemetry_diagnostics.support. com 'dir = out action = block remoteip = 157.56.121.89 enable = yes netsh advfirewall firewall add rule name =' telemetry_corp.sts.microsoft.com 'dir = out action = block remoteip = 131.107.113.238 enable = yes netsh advfirewall firewall add rule name = 'telemetry_statsfe1.ws.microsoft.com' dir = out action = block remoteip = 134.170.115.60 enable = yes netsh advfirewall firewall add rule name = 'telemetry_pre.footprintpredict.com' dir = out action = block remoteip = 204.79. 197.200 enable = yes netsh advfirewall firewall add rule name = 'telemetry_i1.services.social.microsoft.com' dir = out action = block remoteip = 104.82.22.249 enable = yes netsh advfirewall firewall add rule name = 'telemetry_feedback.windows.com' dir = out action = block remoteip = 134.170.185.70 enable = yes netsh advfirewall firewall add rule name = 'telemetry_ feedback.microsoft-hohm.com 'dir = out action = block remoteip = 64.4.6.100,65.55.39.10 enable = yes netsh advfirewall firewall add rule name =' telemetry_feedback.search.microsoft.com 'dir = out action = block remoteip = 157.55.129.21 enable = yes netsh advfirewall firewall add rule name = 'telemetry_rad.msn.com' dir = out action = block remoteip = 207.46.194.25 enable = yes netsh advfirewall firewall add rule name = 'telemetry_preview.msn.com' dir = out action = block remoteip = 23.102.21.4 enable = yes netsh advfirewall firewall add rule name = 'telemetry_dart.l.doubleclick.net' dir = out action = block remoteip = 173.194.113.220,173.194.113.219,216.58.209.166 enable = yes netsh advfirewall firewall add rule name = 'telemetry_ads.msn.com' dir = out action = block remoteip = 157.56.91.82,157.56.23.91,104.82.14.146,207.123.56.252,185.13.160.61,8.254.209.254 enable = yes netsh advfirewall firewall add rule name = 'telemetry_a.ads1.msn.com' dir = out action = block remoteip = 198.78.208.254,185.13.160.61 enable = yes netsh advfirewall firewall add rule name = 'telemetry_global.msads.net.c.footprint.net' dir = out action = block remoteip = 185.13.160.61,8.254.209.254,207.123.56.252 enable = yes netsh advfirewall firewall add rule name = 'telemetry_az361816.vo.msecnd .net 'dir = out action = block remoteip = 68.232.34.200 enable = yes netsh advfirewall firewall add rule name =' telemetry_oca.telemetry.microsoft.com.nsatc.net 'dir = out action = block remoteip = 65.55.252.63 enable = da netsh advfirewall firewall dodaj pravilo ime = 'telemetry_reports.wes.df.telemetry.microsoft.com' dir = out action = block remoteip = 65.52.100.91 enable = yes netsh advfirewall firewall add rule name = 'telemetry_df.telemetry.microsoft.com 'dir = out action = block remoteip = 65.52.100.7 enable = yes netsh advfirewall firewall add rule name =' telemetry_cs1.wpc.v0cdn.net 'dir = out action = block remoteip = 68.232.34.200 enable = yes netsh advfirewall firewall add rule name = 'telemetry_vortex-sandbox.data.microsoft.com' dir = out action = block remoteip = 64.4.54.32 enable = yes netsh advfirewall firewall add rule name = 'tele metry_pre.footprintpredict.com 'dir = out action = block remoteip = 204.79.197.200 enable = yes netsh advfirewall firewall add rule name =' telemetry_i1.services.social.microsoft.com 'dir = out action = block remoteip = 104.82.22.249 enable = yes netsh advfirewall firewall add rule name = 'telemetry_ssw.live.com' dir = out action = block remoteip = 207.46.101.29 enable = yes netsh advfirewall firewall add rule name = 'telemetry_statsfe1.ws.microsoft.com' dir = out action = block remoteip = 134.170.115.60 enable = yes netsh advfirewall firewall add rule name = 'telemetry_msnbot-65-55-108-23.search.msn.com' dir = out action = block remoteip = 65.55.108.23 enable = yes netsh advfirewall požarni zid dodaj pravilo ime = 'telemetry_a23-218-212-69.deploy.static.akamaitechnologies.com' dir = out action = block remoteip = 23.218.212.69 enable = yes
Da bi vam to olajšali in hitro dodali ta pravila, sem za vas pripravil paketno datoteko. Zaženite 'add rules.cmd' in potrdite poziv UAC.
Prenesite datoteko Block Telemetry Rules za sistem Windows 10
Po tem bi morali v požarnem zidu Windows videti naslednje:

Windows 10 vas ne bo več vohunil. Pri tem niso bila uporabljena nobena orodja tretjih oseb.
kako videti nekatere všečke na instagramu
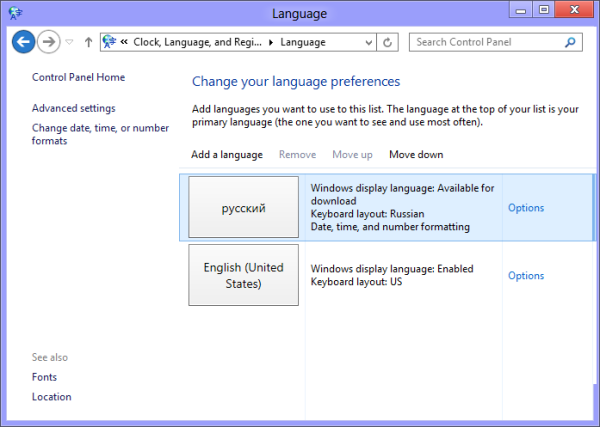
Zdaj pojdite na Storitve in aplikacije -> Storitve v levem podoknu. Na seznamu storitev onemogočite naslednje storitve:
Služba za sledenje diagnostike
dmwappushsvc
Dvokliknite omenjene storitve in izberite »Onemogočeno« za vrsto zagona:
 Moraš znova zaženite Windows 10 da začnejo spremembe veljati.
Moraš znova zaženite Windows 10 da začnejo spremembe veljati.
Ta zadnji korak bo onemogočil 'keylogger', ki morda pošilja vnesene podatke. Ta korak dejansko ni potreben, saj so vsi strežniki že blokirani. Ko pa posodobite sistem Windows 10, lahko Microsoft spremeni seznam strežnikov in doda nove strežnike. Z onemogočanjem omenjenih storitev ste torej lahko prepričani, da OS podatkov ne bo zbiral in pošiljal podatkov na skrivaj.
To je to. Odprta sem za vaša vprašanja. Če česa niste razumeli, mi to sporočite v komentarjih.